-

Wystawy
-

Inne
07 / 06 - 10:00
-

Imprezy
30 / 06 - 18:00
-

Inne
30 / 06 - 18:00
-

Inne
30 / 06 - 18:00
-

Imprezy
01 / 07 - 09:00
-

Warsztaty
Szycie toreb i plecaków | otwarta pracownia krawiecka
01 / 07 - 10:00
Szyjmy torby i plecaki! Naszym materiałem będzie drelich lub ortalion.
Ilość miejsc: 20
Konieczne zapisy!
-

Warsztaty
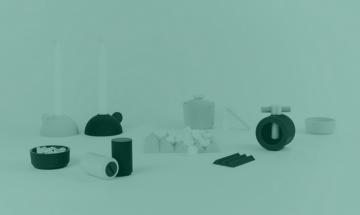
letni warsztat ceramiczny august
01 / 07 - 11:00
Sztorm nadchodzi! august design studio zaprasza na intensywne warsztaty projektowo-ceramiczne.
Ilość miejsc: 12
Konieczne zapisy!
-

Warsztaty
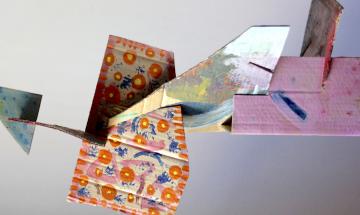
Boa Vista. Design jako narzędzie rozwoju społeczności
01 / 07 - 11:00
Ilość miejsc: 15
Konieczne zapisy!
-
Dla dzieci
01 / 07 - 11:00
-

Warsztaty
01 / 07 - 12:00
Zapraszamy na warsztaty podczas których zdradzimy tajniki makramowych splotów.
Ilość miejsc: 12
Konieczne zapisy!
-

Inne
Oprowadzanie kuratorskie - Miasto na Fali
01 / 07 - 14:00
-

Inne
Oprowadzanie kuratorskie – Peconheiros
01 / 07 - 15:00
-

Wykład
Wykład kuratorski - Let's talk about garbage
01 / 07 - 16:00
-

Imprezy
Wernisaż wystawy Roundabout Baltic
01 / 07 - 18:00
-

Imprezy
Wernisaż wystawy Oskar Zięta – Polskie Projekty Polscy Projektanci
01 / 07 - 18:00
-

Imprezy
Wernisaż #8 - Fajne Chłopaki w Kawiarni TŁOK
01 / 07 - 19:30
-

Warsztaty
Szycie patchworkowych bluz | otwarta pracownia krawiecka
02 / 07 - 10:00
-

Inne
Oprowadzanie kuratorskie - Elementarz polskiego designu
02 / 07 - 11:00
-

Dla dzieci
Forma OBJECT - tworzenie mebli do pokoju dziecięcego
02 / 07 - 11:00
-

Imprezy
Młodzi na Start - Elle Decoration | wernisaż i wręczenie nagrody
02 / 07 - 12:00
-

Dla dzieci
Gra miejska | Poszukiwacze designu
02 / 07 - 12:00
Ilość miejsc: 80
Konieczne zapisy!
-

Warsztaty
Sztorm i oplątwy - tworzenie form do hodowli
02 / 07 - 12:00
Ilość miejsc: 30
Konieczne zapisy!
-

Inne
Młodzi na Start - Elle Decoration | Strefa wiedzy
02 / 07 - 13:00
-

Inne
Oprowadzanie kuratorskie - Oskar Zięta - Polskie Projekty Polscy Projektanci
02 / 07 - 14:00
-

Inne
Spotkanie z twórcami – Dyplomy ASP: Architektura i Wzornictwo 2017
02 / 07 - 15:00
-
Warsztaty
Projektowanie liternictwa do ilustracji
03 / 07 - 10:00
Ilość miejsc: 20
Konieczne zapisy!
-

Warsztaty
03 / 07 - 10:30
-

Warsztaty
03 / 07 - 11:00
-

Dla dzieci
03 / 07 - 11:00
-

Inne
Poznaj Design ze Sztuka Wyboru | food design
03 / 07 - 16:00
-
Wykład
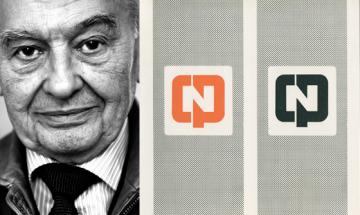
CPN – spuścizna Ryszarda Bojara
03 / 07 - 16:00
-

Wykład
Skok do wody, który odmienił moje życie
03 / 07 - 16:30
Ilość miejsc: 50
Konieczne zapisy!
-

Wykład
Ilustracja nie tylko na papierze
03 / 07 - 17:00
-

Film
03 / 07 - 18:00
-
Wykład
Partycypacja w projektowaniu graficznym
03 / 07 - 18:00
-
Wykład
Projektowanie dla instytucji kultury i sztuki
03 / 07 - 19:00
-

Warsztaty
Re-cover, czyli szycie kurtek dla osób bezdomnych | otwarta pracownia krawiecka
04 / 07 - 10:00
-

Dla dzieci
04 / 07 - 10:00
Ilość miejsc: 20
Konieczne zapisy!
-

Warsztaty
04 / 07 - 10:00
Ilość miejsc: 15
Konieczne zapisy!
-

Warsztaty
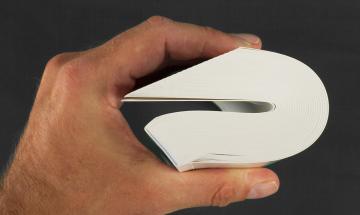
Nurkowanie na wózku inwalidzkim. Projektowanie bez ograniczeń
04 / 07 - 10:00
Ilość miejsc: 20
Konieczne zapisy!
-

Warsztaty
Samochód – od pomysłu do wdrożenia
04 / 07 - 10:00
Dowiedź się, jaką drogę musi przejść produkt, nim uda się go w pełni zrealizować.
Ilość miejsc: 20
Konieczne zapisy!
-

Inne
II Oprowadzanie kuratorskie - Elementarz polskiego designu
04 / 07 - 11:00
-
Warsztaty
Creative Coding, czyli kod tworzywem projektanta
04 / 07 - 14:00
Kodowanie w rękach projektanta staje się niezwykłym narzędziem kreacji.
Ilość miejsc: 20
Konieczne zapisy!
-

Warsztaty
04 / 07 - 14:00
-

Inne
Poznaj Design ze Sztuką Wyboru | future
04 / 07 - 16:00
-

Wykład
Klienci szukają jakości – fenomen czarnej butelki The Haze
04 / 07 - 16:00
-

Inne
Oprowadzanie kuratorskie MANUBA – kolekcja GDD
04 / 07 - 17:00
-

Wykład
Design demokratyczny w nowej Europie
04 / 07 - 17:00
-

Film
Przegląd filmowy: Tylko kochankowie przeżyją
04 / 07 - 18:00
-

Wykład
Bity, atomy i namacalne interfejsy
04 / 07 - 18:00
-

Wykład
Zgadywanie w sprzedaży się nie opłaca
04 / 07 - 18:00
Ilość miejsc: 50
Konieczne zapisy!
-

Wykład
Life after food (as we know it)
04 / 07 - 19:00
-

Inne
Wnętrza biurowe podnoszące wyniki pracy | konsultacje projektowe
05 / 07 - 10:00
Czasy, gdy pracowaliśmy w typowo biurowej atmosferze, dobiegły już końca.
Ilość miejsc: 8
Konieczne zapisy!
-

Inne
Projektowanie w drewnie | konsultacje projektowe
05 / 07 - 10:00
-

Inne
Sztorm w Twojej firmie! Konsultacje projektowe
05 / 07 - 10:00
-

Warsztaty
Marketing „zrób to sam“- skuteczna sprzedaż w branży kreatywnej
05 / 07 - 10:00
-

Inne
05 / 07 - 11:00
-

Dla dzieci
05 / 07 - 11:00
-

Warsztaty
05 / 07 - 12:00
-

Inne
Poznaj Design ze Sztuka Wyboru | edukacja
05 / 07 - 16:00
-

Wykład
Woonerf – czy nadciąga miejska rewolucja?
05 / 07 - 17:00
-

Film
Przegląd filmowy: Vicky Cristina Barcelona
05 / 07 - 18:00
-

Wykład
Jak wyzwolić zespołową kreatywność?
05 / 07 - 18:00
-

Wykład
05 / 07 - 19:00
-

Film
Uzdrowisko. Architektura Zawodzia
05 / 07 - 20:00
-

Warsztaty
Szturmiaki, czyli stroje-manifesty | otwarta pracownia krawiecka
06 / 07 - 10:00
Ilość miejsc: 20
Konieczne zapisy!
-

Warsztaty
Brainstorming w projektowaniu usług i produktów
06 / 07 - 10:00
Z 2000 pomysłów powstaje tylko 11 doskonałych rozwiązań i około 17 względnie dobrych.
Ilość miejsc: 16
Konieczne zapisy!
-

Warsztaty
Nie tylko wizerunek. Jak sprzedawać w mediach społecznościowych
06 / 07 - 10:00
-
Dla dzieci
Globus - tworzenie przestrzennych map
06 / 07 - 11:00
Ilość miejsc: 30
Konieczne zapisy!
-

Dla dzieci
06 / 07 - 13:00
-

Warsztaty
Miasto na fali - jak powstaje i smakuje miejski miód
06 / 07 - 14:00
-

Warsztaty
Design thinking - wzmocnij swoją kreatywną pewność
06 / 07 - 15:00
Ilość miejsc: 30
Konieczne zapisy!
-

Imprezy
Napijmy się z kubków BIRDS w kawiarni TŁOK!
06 / 07 - 16:00
-

Wykład
Opakowania. Jak projektować, żeby recyklingować?
06 / 07 - 16:00
-

Dla dzieci
06 / 07 - 17:00
-

Wykład
Upcykling jako innowacyjny trend w sztuce, designie i odpowiedzialnym biznesie
06 / 07 - 17:00
-

Film
Przegląd filmowy: Wszystkie nieprzespane noce
06 / 07 - 18:00
-

Wykład
Otręby. Przyszłość jednorazówek
06 / 07 - 18:00
-

Inne
EcoDesign Circle | panel dyskusyjny
06 / 07 - 19:00
-

Wykład
Design językiem Biznesu | spotkania&warsztaty
07 / 07 - 09:00
Ilość miejsc: 300
Konieczne zapisy!
-

Inne
07 / 07 - 10:00
-

Dla dzieci
Design na fali - animacja poklatkowa
07 / 07 - 10:00
Ilość miejsc: 10
Konieczne zapisy!
-

Dla dzieci
07 / 07 - 13:00
Czy place zabaw dla dzieci mogłyby być zaprojektowane przez dzieci?
Ilość miejsc: 15
Konieczne zapisy!
-

Dla dzieci
Zostań projektantem! | tura II
07 / 07 - 17:00
-

Wykład
O relacjach między przedmiotami – wykład Agnieszki Jacobson-Cieleckiej
07 / 07 - 18:00
-

Wykład
12 kroków do stworzenia marki osobistej
07 / 07 - 19:00
-

Inne
08 / 07 - 10:00
-

Warsztaty
Upcycling, czyli nowe życie starych rzeczy | otwarta pracownia krawiecka
08 / 07 - 10:00
-

Warsztaty
Fotografia wnętrz dla projektantów
08 / 07 - 10:00
-

Warsztaty
08 / 07 - 10:00
-

Warsztaty
Idź na żywioł - narratologia dla zawodów kreatywnych
08 / 07 - 10:30
-

Warsztaty
08 / 07 - 12:30
Ilość miejsc: 25
Konieczne zapisy!
-

Dla dzieci
08 / 07 - 13:00
Czy place zabaw dla dzieci mogłyby być zaprojektowane przez dzieci?
Ilość miejsc: 15
Konieczne zapisy!
-

Inne
II Oprowadzanie kuratorskie - Miasto na fali
08 / 07 - 14:00
-

Wykład
08 / 07 - 15:00
-

Wykład
Jak stworzyć unikalną markę handmade?
08 / 07 - 15:00
-

Warsztaty
Benjamin Moore - zmieniamy sposób patrzenia na kolory
08 / 07 - 15:00
-

Warsztaty
Tworzenie wizualizacji architektonicznych w oparciu o nowoczesne programy graficzne
08 / 07 - 15:00
-

Wykład
Niderlandzkie wzornictwo powojenne
08 / 07 - 16:00
-

Dla dzieci
Zostań projektantem! | tura III
08 / 07 - 17:00
-

Wykład
Strukturalny sztorm we wnętrzach – raport trendów 2017/ 2018 wg Ceramiki Paradyż
08 / 07 - 17:00
-
Inne
Oprowadzanie kuratorkie - RE:MAIN - Przetrwanie
08 / 07 - 18:00
-

Wykład
Jak pracuje się w najlepszym biurze na świecie?
08 / 07 - 18:00
-

Wykład
Otworzymy jak skończymy - projektowanie w gastronomii
08 / 07 - 19:00
-

Inne
09 / 07 - 10:00
-

Dla dzieci
Sztormowisko - pracownia tworzenia multimedialnych opowieści przy użyciu technologii
09 / 07 - 11:00
Sztormowisko to kurs praktycznego zastosowania technologii dla młodzieży.
Ilość miejsc: 15
Konieczne zapisy!
-

Warsztaty
Rejs okrętem Bonzai - metoda planowania nielinearnego
09 / 07 - 12:00
-

Inne
Oprowadzanie kuratorskie - Roundabout Baltic
09 / 07 - 14:00
-

Wykład
09 / 07 - 14:00